EP-0149
TPM9670 Module for Raspberry Pi
Descriptions
TPM is an add-on GPIO TPM module for the Raspberry Pi platform based on an Infineon Optiga™ SLB 9670 TPM 2.0 . It is compatible with all Raspberry Pi models including the Raspberry Pi 4. Device tree overlay support with Raspbian Kernel >= 4.14.85 We offer customization services / custom designs starting at just 100 units. The module is compatible with Windows 10 IoT (on Pi 2 / 3). It is shipped with firmware versions >= 7.85 for TPM 2.0.
A TPM is a cryptographic processor present on most commercial PCs and servers. Ubiquitous in nature, it can be used for a wide variety of use cases, such as storing keys for VPN access and encryption keys for hard disks, or preventing dictionary attacks to retrieve private keys. While a typical TPM provides several cryptographic capabilities, three key features are relevant for this post:
- Establishing a root of trust
- Secure boot
- Device identification
Secure boot
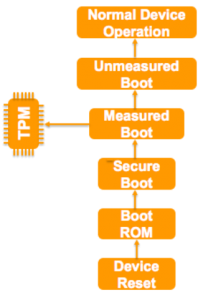
A secured boot builds on the underlying notion of a root of trust to protect the boot process from being compromised on the device. This whole process by which the trustworthiness of a device is established right from the chip is called a “Secure Boot”. In case a chain of trust is broken, the boot process is aborted and the device attempts to go back to its last known good state. An extension to secured boot process is a measured boot – where the device does not halt the boot process. Instead, it records the identity of each component that participates in the boot process so that these component identities can be verified later against a list of approved component identities for that device. This is called a measured boot. These two processes are illustrated in the following diagram.
Typical sequence of a measured boot
A typical sequence of a measured boot is as follows:
- The boot ROM acts as the root of trust.
- Upon a device reset, each image that forms part of the boot sequence is validated (measured) before execution.
- The measurements are stored in a TPM.
- Each measurement serves as the proxy for the root of trust for the subsequent step in the boot sequence.
- Normally, only critical and security-sensitive process and configuration files are considered for the measurement.
- After the security-sensitive processes are completed, the device enters the unmeasured boot stage before entering normal system operation state.
Device identification
In IoT solution deployments, it is important to check the identity of the device that is communicating with the messaging gateway. The usual method is to generate key pairs for the devices, which are then used to authenticate and encrypt the traffic. However, key pairs residing on the disk are susceptible to tampering. The TPM steps in here by storing the keys in tamper-resistant hardware. The keys are generated inside the TPM itself and are thereby protected from being retrieved by external programs. In fact, even without harnessing the capabilities of a hardware root of trust and secure boot, the TPM is also valuable just as a hardware key store. The private keys are protected by the hardware and offer far better protection than a software key.
Features
- Easy to install
- Infineon Optiga™ SLB 9670 TPM 2.0
- Konform mit TPM Spezifikation 2.0 Rev. 01.38
- Firmware >= 7.85
- TRNG (Echter Zufallszahlengenerator) - True Hardware Random Number Generator
- Storing keys for VPN access
- Encryption keys for hard disks
- Preventing dictionary attacks to retrieve private keys
Specifications
Package Includes
How to use
Documentations
- TPM Software: [ https://github.com/tpm2-software ]
- ELTT2 tool: [ https://github.com/Infineon/eltt2 ]
- Useful scripts: [ https://github.com/PaulKissinger/LetsTrust ]
- Work with AWS Greengrass IoT : [ https://aws.amazon.com/cn/blogs/iot/using-a-trusted-platform-module-for-endpoint-device-security-in-aws-iot-greengrass/ ]
- Datasheet: [ https://www.infineon.com/dgdl/Infineon-OPTIGA_TPM-PB-v10_15-EN.pdf?fileId=5546d46145da30e80145efa2f0b96a8e ]
- Datasheet(HTML): [ https://www.digikey.cn/zh/htmldatasheets/production/2078094/0/0/1/optiga-tpm-brief.html ]
Keywords
- TPM9670 Module, Trusted Platform module, Raspberry Pi, SLB 9670, SLI 9670 and SLM 9670